Rainbow 6 Hack Crack Wifi
Hack Like a Pro: How to Crack Passwords. How to Hack Wi-Fi. How Hackers Take Your Encrypted Passwords & Crack Them Rainbow Tables. Jun 20, 2018 - Just for fun tho, connect using WiFi while inside a match plug in your ethernet cable. All operator unlocked for that match. Fyi, this is just a.
Think you have a strong password? Hackers crack 16-character passwords in less than an HOUR
Astalavista
- During an experiment for Ars Technica hackers managed to crack 90% of 16,449 hashed passwords
- Six passwords were cracked each minute including 16-character versions such as 'qeadzcwrsfxv1331'
We are 100% sure Rainbow Six Siege Hacks. Cheats crack DIY download Easy Free game gameplay Games gaming Get Hack hacker hacking hacks hack wifi hack wifi key hack.
Published: 17:17 BST, 28 May 2013 Updated: 18:15 BST, 28 May 2013
A team of hackers has managed to crack more than 14,800 supposedly random passwords - from a list of 16,449 - as part of a hacking experiment for a technology website.
The success rate for each hacker ranged from 62% to 90%, and the hacker who cracked 90% of hashed passwords did so in less than an hour using a computer cluster.
The hackers also managed to crack 16-character passwords including 'qeadzcwrsfxv1331'.
A team of hackers have managed to crack more than 14,800 cryptographically hashed passwords - from a list of 16,449 - as part of a hacking experiment for tech website Ars Technica. The success rate for each hacker ranged from 62% to 90%, including 16-character passwords with a mix of numbers and letters. The hacker who cracked 90% of hashed passwords did so in less than an hour
HACKING JARGON EXPLAINED
Hashed passwords - Hashing takes each user's plain text password and runs it through a one-way mathematical function.
This creates a unique string of numbers and letters called the hash.
Hashing makes it difficult for an attacker to move from hash back to password and it lets sites keep a list of hashes, rather than plain text passwords.
Secret of success in hindi. This means if a list is stolen, the plain text passwords can't be obtained easily.
Cryptographic salt - Sites will add cryptographic salt to passwords to make them harder to crack.
This includes adding random numbers, characters or letters to the start or end of a password during the hashing process so hackers can't automatically enter a six-letter word, for example, and match the hash automatically.
Rainbow tables - A rainbow table is a precomputed table for reversing cryptographic hash functions, usually for cracking password hashes.
Tables are usually used in recovering the plaintext password, up to a certain length consisting of a limited set of characters.
The hackers, working for the website Ars Technica, have now published how they cracked the codes and the traditional methods used to create an anatomy of a hack.
Rather than repeatedly entering passwords into a website, the hackers used a list of hashed passwords they managed to get online.
Hashing takes each user's plain text password and runs it through a one-way mathematical function.
This creates a unique string of numbers and letters called the hash.
Hashing makes it difficult for an attacker to move from hash back to password and it lets sites keep a list of hashes, rather than storing them insecurely as plain-text passwords.
This means if a list is stolen, the plain text passwords can't be obtained easily.
However, this experiment shows this doesn't mean its impossible.
When a user types a password into an online form or service, the system hashes the entered word and checks it against the user's stored, pre-hashed password.
When the two hashes match, the user is allowed entry to their account.
And using characters, a mix of lower and upper case letters and numbers creates slight variations of a hash.
The example, Ars Technica use is: hashing the password 'arstechnica' produced the hash c915e95033e8c69ada58eb784a98b2ed.
Adding capital letters to make 'ArsTechnica' becomes 1d9a3f8172b01328de5acba20563408e after hashing.
Jeremi Gosney, the founder and CEO of Stricture Consulting Group, managed to crack the first 10,233 hashes, or 62 percent of the leaked list, in 16 minutes.
He used a so-called 'brute-force crack' for all passwords that were one to six characters long.
Share this article
Brute-force attacks is when a computer tries every possible combination of six letters and characters, starting with 'a' and ending with '//////.'
It took Gosney just two minutes and 32 seconds to complete the first round, which found 1,316 plain-text passwords.
Gosney then used brute-force to crack all passwords seven or eight characters long that only contained lower letters. This yielded 1,618 passwords.
He repeated this for seven and eight-letter passwords using only upper-case letters to reveal another 708 passwords.
This graph shows how long in days it took the Ars Technica hackers to crack the list of 16,449 hashed passwords based on the method used. It also shows how long it took to crack passwords based on how long they were. Each hacker used a combination of wordlists, brute-force attacks and Markov chains to crack the list. One hacker managed to crack 90% of the list
Using passwords that contained only numbers, from one to 12 digits long, Gosney managed to brute-force 312 passwords in three minutes and 21 seconds.
Gosney has spent years perfecting word lists that contain a list of all the six-letter words, for example, to make cracking the weaker passwords faster.
One hurdle Gosney had to jump during stage one of the hack was 'salted hashes', a technique where sites add random characters to passwords to make them harder to crack.
This can include adding random numbers, characters or letters to the start or end of a password during the hashing process so hackers can't automatically enter a six-letter word, for example, and match the hash automatically.
However, Gosney explained that once one weak, 'cryptographically salted' hashes are cracked it becomes easier to work out the rest.
Once Gosney had obtained the weaker passwords, even those that had been salted, using brute-force he moved onto stage two.
Using a hybrid attack - which combines a dictionary attack with a brute-force attack - he added all possible two-character strings of both numbers and symbols to the end of each word in his dictionary.
Jeremi Gosney used a mixture of brute-force attacks, a hybrid attack that combined wordlists with brute-force attempts, statistically generated guesses using Markov chains, and other rules to turn a list of hashed passwords into plain text. It took him 14 hours and 59 minutes to complete all stages
MORE HACKING JARGON EXPLAINED
Markov chains - This method uses previously cracked passwords and a statistically generated brute-force attack that makes educated guesses to analyse plains and determine where certain types of characters are likely to appear in a password.
A Markov attack on a seven-letter password has a threshold of 65 tries; using the 65 most likely characters for each position.
And because passwords usually have capital letters at the start, lower-case letters in the middle, and symbols and numbers at the end, Markov attacks can crack almost as many passwords as a straight brute-force.
Brute-force attack -Brute force also known as brute force cracking is a trial-and-error method used by to get plain-text passwords from encrypted data.
Just as a criminal might break into, or 'crack' a safe by trying many possible combinations, a brute-force cracking attempt goes through all possible combinations of characters in sequence.
In a six-letter attack, the hacker will start at 'a' and end at '//////'
He recovered 585 plain passwords in 11 minutes and 25 seconds.
He next added all possible three-character strings to get another 527 hashes in 58 minutes to complete.
Thirdly, he added all four-digit number strings and he took 25 minutes to recover 435 passwords.
In round four he added all possible strings containing three lower-case letters and numbers and got 451 more passwords.
In five hours and 12 minutes he managed to get 2,702 passwords.
He continued to crack the rest of the passwords using a hybrid attack and cracked a total of 12,935 hashes, or 78.6 percent of the list, in five hours and 28 minutes.
During the third stage, in which Gosney attempted to crack the most complicated passwords, he used a mathematical system known as Markov chains.
This method uses previously cracked passwords and a statistically generated brute-force attack that makes educated guesses to analyse plain text passwords, and determine where certain types of characters are likely to appear in a password.
A Markov attack on a seven-letter password has a threshold of 65 tries; using the 65 most likely characters for each position.
And because passwords usually have capital letters at the start, lower-case letters in the middle, and symbols and numbers at the end, Markov attacks can crack almost as many passwords as a straight brute-force.
Hackers use a mix of wordlists, rainbow tables (pictured) and an algorithm called a Markov chains, among other techniques, to crack passwords from a hashed list. A rainbow table is a precomputed table for reversing cryptographic hash functions, usually for cracking password hashes. Tables are usually used in recovering the plaintext password, up to a certain length consisting of a limited set of characters
TYPES OF PASSWORDS RECOVERED
Some of the longer, stronger and more noticeable passwords that the hackers were able to recover included:
k1araj0hns0n
Sh1a-labe0uf
Apr!l221973
Qbesancon321
DG091101%
@Yourmom69
ilovetofunot
windermere2313
tmdmmj17 and
BandGeek2014
Also included in the list were:
all of the lights
i hate hackers
allineedislove
ilovemySister31,
iloveyousomuch
Philippians4:13
Philippians4:6-7 and
qeadzcwrsfxv1331
From this method, Gosney discovered that people who don't know each other use very similar, and in some cases, identical passwords for the same sites.
During this third stage, Gosney also used other wordlists and rules and it took Gosney 14 hours and 59 minutes to complete all stages.
He managed to get another 1,699 more passwords - three hours to cover the first 962 plain passwords in this stage and 12 hours to get the remaining 737.
The other two password experts who cracked this list used many of the same techniques and methods, although not in the same sequence and with different tools.
They used a wordlist that was created directly from the 2009 breach of online games service RockYou.
This hack leaked more than 14 million unique passwords in plain text and this list is the largest list of 'real-world passwords ever to be made public.'
This method cracked 4,900 of the passwords. The same list was then used again, but this time the last four letters of each word were replaced with four digits. This yielded 2,136 passcodes.
Hacker radix then tried brute-forcing all numbers, starting with a single digit, then two digits, then three digits, and so, and managed to recover 259 additional passwords.
He then ran the 7,295 plain text passwords he'd recovered through the Password Analysis and Cracking Toolkit, developed by password expert Peter Kacherginsky, to identify patterns.
A 25-computer cluster that can cracks passwords by making 350 billion guesses per second. It was unveiled in December by Jeremi Gosney, the founder and CEO of Stricture Consulting Group. It can try every possible Windows passcode in the typical enterprise in less than six hours to get plain-text passwords from lists of hashed passwords
Radix then used this information to run a mask attack, which uses the same methods as Gosney's hyrbid attack but took less time.
He replaced common letters with numbers, for example he replaced 'e' with the '3' and recovered 1,940 passwords.
In December, Gosney created a 25-computer cluster that can make 350 billion guesses a second.
In an email to Ars Technica, Gosney explained: 'Normally I start by brute-forcing all characters from length one to length six because even on a single GPU, this attack completes nearly instantly with fast hashes.
'And because I can brute-force this really quickly, I have all of my wordlists filtered to only include words that are at least six chars long.
'This helps to save disk space and also speeds up wordlist-based attacks.
'Same thing with digits. I can just brute-force numerical passwords very quickly, so there are no digits in any of my wordlists.
'Then I go straight to my wordlists + best64.rule since those are the most probable patterns, and larger rule sets take much longer to run.
'Our goal is to find the most plains in the least amount of time, so we want to find as much low-hanging fruit as possible first.'
Learn how to attack wireless networks
Learn about exploiting wireless networks, including protocols, Wi-Fi authentication and weak points, as well as an overview of mobile devices.
Get started today
Internet is now the basic need of our daily life. With the increasing use of smartphones, most of the things are now online. Every time we have to do something, we just use our smartphone or desktop. This is the reason wi-fi hotspots can be found everywhere.
People also use wireless in their home network to connect all devices. Every person can see the neighborhood wi-fi networks in the system, and they want to use it for free. But most these networks are secured with a password key. You need to know this security key to access the network. When your own network is down, you will desperately want to connect to these neighborhood networks. For this, people generally search for wi-fi password cracking tools to get unauthorized access to those wireless networks.
Sometimes when you are on a network, you also want to check what is happening on the network. This happens mostly in big organizations, when an employer wants to check who is doing what in the network. For these things, there are a few network hacking tools available that let users analyze packets and see what other users are doing.
In this article, I am going to discuss wireless security and best wi-fi password cracking or recovery tools. I will explain the kind of encryption wireless networks use and how these tools can crack the networks to get access. We will also see what tools let users monitor networks.
Wireless Networks and Hacking
Wireless networks are based on IEEE 802.11 standards defined by IEEE(Institute of Electrical and Electronics Engineers) for ad hoc networks or infrastructure networks. Infrastructure networks have one or more access points which coordinate the traffic between the nodes. But in ad hoc networks, there is no access point; each node connects in a peer-to-peer way.
Basically there are two types of vulnerabilities which can be found in the Wireless LAN. One is poor configuration and the other is poor encryption. Poor configuration is caused by the network admin who manages the network. It may include the weak password, no security settings, use of default configurations, and other user related things. Poor encryption is related to security keys used to protect the wireless network. It is there because of issues in WEP or WPA.
WEP and WPA
WEP and WPA are the two main security protocols used in Wi-Fi LAN. WEP is known as Wired Equivalent Privacy (WEP). It is a deprecated security protocol which was introduced back in 1997 as a part of original 802.11 standards. But it was weak, and several serious weakness were found in the protocol. Now, this can be cracked within minutes. So, a new kind of security protocol was introduced in 2003. This new protocol was Wi-Fi Protected Access (WPA). It has mainly two versions, 1 and 2 (WPA and WPA2). Now it is the current security protocol used in wireless networks. To get unauthorized access to a network, one needs to crack these security protocols. There are many tools which can crack Wi-Fi encryption. These tools can either take advantage of WEP weaknesses or use bruteforce attacks on WPA/WPA2. I am sure now you know that you should never use WEP security.
Basically wireless hacking tools are of two types. One of which can be used to sniff the network and monitor what is happening in the network. And other kinds of tools are used to hack WEP/WPA keys. These are the popular tools used for wireless password cracking and network troubleshooting.
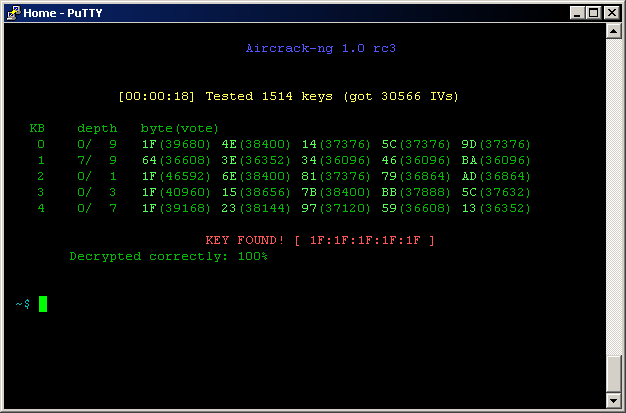
1. Aircrack
Aircrack is one of the most popular wireless passwords cracking tools which you can use for 802.11a/b/g WEP and WPA cracking. Aircrack uses the best algorithms to recover wireless passwords by capturing packets. Once enough packets have been gathered, it tries to recover the password. To make the attack faster, it implements a standard FMS attack with some optimizations.
The company behind the tool also offers an online tutorial where you can learn how to install and use this tool to crack wireless passwords. It comes as Linux distribution, Live CD and VMware image options. You can use any of these. It supports most of the wireless adapters and is almost guaranteed to work. If you are using a Linux distribution, the only drawback of the tool is that it requires deeper knowledge of Linux. If you are not comfortable with Linux, you will find it hard to use this tool. In this case, try Live CD or VMWare image. VMWare Image needs less knowledge, but it only works with a limited set of host OS, and only USB devices are supported.
Before you start using this too, confirm that the wireless card can inject packets. Then start WEP cracking. Read the online tutorial on the website to know more about the tool. If you will follow steps properly, you will end up getting success with this tool.
Download: http://www.aircrack-ng.org/
2. AirSnort
AirSnort is another popular tool for decrypting WEP encryption on a wi-fi 802.11b network. It is a free tool and comes with Linux and Windows platforms. This tool is no longer maintained, but it is still available to download from Sourceforge. AirSnort works by passively monitoring transmissions and computing encryption keys once it has enough packets received. This tool is simple to use. If you are interested, you can try this tool to crack WEP passwords.
Download: http://sourceforge.net/projects/airsnort/
3. Cain & Able
Cain & Able is a popular password cracking tool. This tool is developed to intercept network traffic and then discover passwords by bruteforcing the password using cryptanalysis attack methods. It can also recover wireless network keys by analyzing routing protocols. It you are trying to learn wireless security and password cracking, you should once try this tool.
Download: http://www.oxid.it/cain.html
4. Kismet
Kismet is the wi-fi 802.11 a/b/g/n layer2 wireless network sniffer and IDS. It works with any wi-fi card which supports rfmon mode. It passively collects packets to identify networks and detect hidden networks. It is built on client/server modular architecture. It is available for Linux, OSX, Windows and BSD platforms.
Download: http://www.kismetwireless.net/
5. NetStumbler
NetStumbler is a popular Windows tool to find open wireless access points. This tool is free and is available for Windows. A trimmed down version of the tool is also available. It is called MiniStumbler.
Basically NetStumblet is used for wardriving, verifying network configurations, finding locations with a poor network, detecting unauthorized access points, and more.
But the tool also has a big disadvantage. It can be easily detected by most of the wireless intrusion detection systems available. This is because it actively probes a network to collect useful information. Another disadvantage of the tool is that it does not work properly with the latest 64 bit Windows OS. This is because the tool was last updated back in April 2004. It has been around 11 years since the last stable release of the tool.
Download Netstumbler: http://www.stumbler.net/
6. inSSIDer
inSSIDer is a popular Wi-Fi scanner for Microsoft Windows and OS X operating systems. Initially the tool was opensource. Later it became premium and now costs $19.99. It was also awarded as “Best Opensource Software in Networking”. The inSSIDer wi-fi scanner can do various tasks, including finding open wi-fi access points, tracking signal strength, and saving logs with GPS records.
Download inSSIDer: http://www.inssider.com/
7. WireShark
WireShark is the network protocol analyzer. It lets you check what is happening in your network. You can live capture packets and analyze them. It captures packets and lets you check data at the micro-level. It runs on Windows, Linux, OS X, Solaries, FreeBSD and others. WireShark requires good knowledge of network protocols to analyze the data obtained with the tool. If you do not have good knowledge of that, you may not find this tool interesting. So, try only if you are sure about your protocol knowledge.
Download Wireshark: https://www.wireshark.org/
8. CoWPAtty
CoWPAtty is an automated dictionary attack tool for WPA-PSK. It runs on Linux OS. This program has a command line interface and runs on a word-list that contains the password to use in the attack.
Using the tool is really simple, but it is slow. That’s because the hash uses SHA1 with a seed of SSID. It means the same password will have a different SSIM. So, you cannot simply use the rainbow table against all access points. So, the tool uses the password dictionary and generates the hack for each word contained in the dictionary by using the SSID.
The new version of the tool tried to improve the speed by using a pre-computed hash file. This pre-computed file contains around 172000 dictionary file for around 1000 most popular SSIs. But if your SSID is not in those 1000, you are unlucky.
Download CoWPAtty: http://sourceforge.net/projects/cowpatty/
9. Airjack
Airjack is a Wi-Fi 802.11 packet injection tool. This wireless cracking tool is very useful in injecting forged packets and making a network down by denial of service attack. This tool can also be used for a man in the middle attack in the network.
Download AirJack: http://sourceforge.net/projects/airjack/
10. WepAttack
WepAttack is an open source Linux tool for breaking 802.11 WEP keys. This tool performs an active dictionary attack by testing millions of words to find the working key. Only a working WLAN card is required to work with WepAttack.
Download WebAttack: http://wepattack.sourceforge.net/
11. OmniPeek
OmniPeek is another nice packet sniffer and network analyzer tool. This tool is commercial and supports only Windows operating systems. This tool is used to capture and analyze wireless traffic. But it requires you to have good knowledge of protocols to properly understand things. A good thing is that the tool works with most of the network interface cards available in market. This tool is used for network troubleshooting. This tool also supports plugins, and 40 plugins are already available to extend the features of the tool.
Download: http://www.wildpackets.com/products/distributed_network_analysis/omnipeek_network_analyzer
12. CommView for WiFi
CommView for WiFi is another popular wireless monitor and packet analyzer tool. It comes with an easy to understand GUI. It works fine with 802.11 a/b/g/n/ac networks. It captures every packet and displays useful information as a list. You can get useful information like access points, stations, signal strength, network connections and protocol distribution.
Captured packets can be decrypted by user-defined WEP or WPA keys.
This tool is basically for wi-fi network admins, security professionals, and home users who want to monitor their wi-fi traffic and programmers working on software for wireless networks.
Download CommView: http://www.tamos.com/products/commwifi/
13. CloudCracker
CloudCracker is the online password cracking tool for cracking WPA protected wi-fi networks. This tool can also be used to crack different password hashes. Just upload the handshake file, enter the network name and start the tool. This tool has a huge dictionary of around 300 million words to perform attacks.
Try Cloudcracker: https://crack.sh/
Ethical Hacking Training
Conclusion
In this post, I discussed 13 wireless hacking tools. A few wireless hacking tools are for cracking the password to get unauthorized access, and a few are for monitoring and troubleshooting the network. But most of the people really interested in tools to crack wireless hotspots just want to get free Internet access.
The above collection also contains those tools which try a dictionary attack to crack wi-fi passwords to allow you to get free Internet access. But be sure not to use these tools in a risky place. Hacking wireless networks to get unauthorized access may be a crime in your country. You may get into trouble for using these tools. So, please do not use these tools for illegal works. As I already mentioned, you should never use the WEP encryption key in your home or wireless network. With available tools, it is child’s play to crack the WEP keys and access your wi-fi network.
Wireless monitoring and troubleshooting tools are basically for network admins and programmers working on wi-fi based software. These tools really help when some of your systems face problems in connecting to the network.
I hope you enjoyed this article and got relevant information about popular wireless hacking and password cracking tools. I tried my best to compile this list of password hacking tools, but as a human error, I may miss something. If I forgot any important tool in this, please let me know in the comments.